News
Grasping Tech Demise: Your Ultimate Guide

Tech demis are constantly changing in the tech industry. “Tech demise” may sound negative, but it is an important part of technology’s development. In this article, we will explore the cycle of technological obsolescence and renewal that shapes our modern world.
UNDERSTANDING THE EVOLUTION OF TECHNOLOGY
Technology advances quickly, making old tools and infrastructure obsolete. Businesses strive to stay ahead by constantly innovating.
Transitioning Away from Outdated Technologies
For several reasons, formerly useful technology has fallen out of use. It’s conceivable that they might struggle to meet the demands of contemporary consumers, or that meeting those demands would incur significant costs. For companies heavily invested in outdated technologies, this phase of technological decline can prove especially challenging.The Emergence of Cutting-Edge Technologies
New technologies replace older ones. Consumers and tech fans find this exciting because of the availability of cutting-edge technology and enhanced user experiences.
Effects of Technological Obsolescence on Businesses
The impact of a dying tech demis on businesses can be significant. They must transition to the new system, invest in retraining employees, and transfer data. Failing to do so can result in decreased productivity and competitiveness.
Navigating Evolving Technological Landscapes
Technology companies must be flexible to succeed. They should regularly evaluate their current technology and be ready to invest in innovative solutions. Adaptability is key.
Importance Of Staying Updated
Tech organizations must prioritize updates to remain relevant and competitive. Regular updates ensure product safety, peak performance, and alignment with consumer needs.
The Role of Human Factors in Technological Obsolescence
Technology failure is not limited to individual hardware. People’s ability to use these technologies in their daily lives and jobs is also at risk. It is crucial to provide adequate assistance and instruction during these times of change.
Balancing Tradition And Innovation
Keeping useful technology is just as important as adopting new ones. Finding the balance between stability and change can be a challenge for many businesses.
Obstacles Encountered by Tech Enterprises
The tech industry faces various challenges such as competition, changing client preferences, and cybersecurity risks. To have a successful career in technology, it is crucial to navigate these obstacles effectively.
Lessons From Tech Demise
Technologies can fail, reminding us of their impermanence. Businesses that don’t innovate or become complacent will become irrelevant.
The Influence of Consumer Choices
Consumers’ choices greatly impact the decline of technologies. If people desire new features or technologies, companies must retire outdated systems.
Sustainable Tech Evolution
The tech sector is becoming more aware of the importance of environmental responsibility. Businesses are facing growing pressure to offer eco-friendly products and procedures to address the impact of the upcoming technological collapse.
Conclusion:
Tech demis constantly evolve, making obsolescence unavoidable. To stay relevant, businesses and individuals must embrace new technologies while respecting the past.
FAQs
What causes old technologies to become obsolete?
Older technologies become obsolete due to their inability to meet new standards, declining economic viability, and changing consumer preferences.
HOW DO BUSINESSES NAVIGATE TECH DEMISE?
To avoid technological obsolescence, companies should maintain a cutting-edge presence, adopt cutting-edge technologies, and thoroughly train their staff.
WHY IS IT ESSENTIAL FOR TECH COMPANIES TO BALANCE TRADITION AND INNOVATION?
Companies that find a balance between history and innovation can keep the best aspects of old technologies while progressing.
Related Articles:
News
Did Helen Keller Fly a Plane: A Complete Story
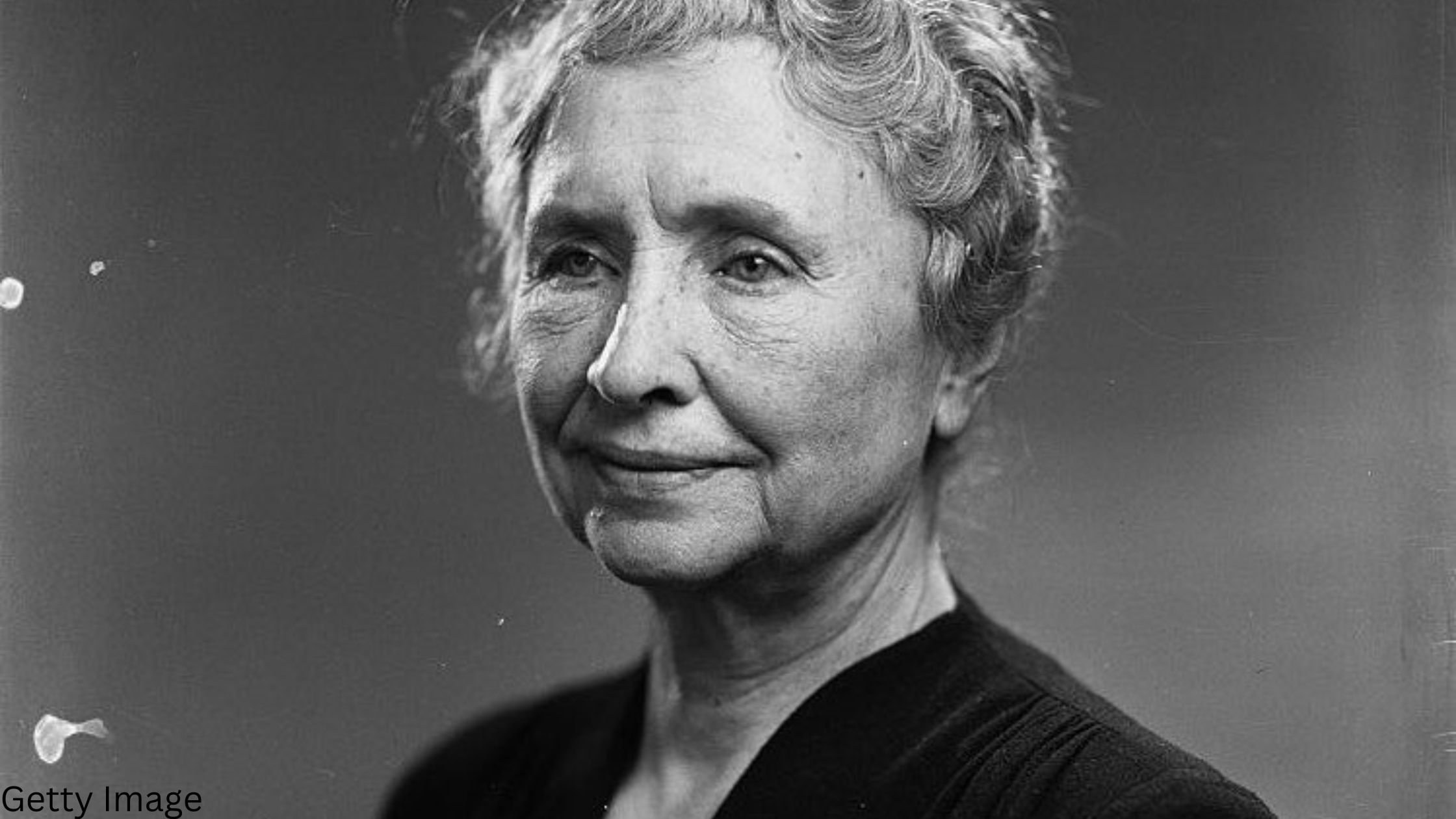
In June 1946, an extraordinary event unfolded as an airplane journeyed from Rome to Paris, with an exceptional passenger taking the role of the pilot. This remarkable passenger was none other than Dr. Helen Keller, a renowned American writer, educator, and activist who overcame the challenges of being blind and deaf since childhood.
Early Adventures: Keller’s First Flight as a Passenger (1919)
Explore Helen Keller’s initial encounter with flight during the filming of “Deliverance” in 1919. Despite script discrepancies, Keller’s enthusiasm for the opportunity to fly was evident.
Embracing Technological Progress: Keller’s Aerial Journeys
Witness how, with advancements in aviation technology, Helen Keller seized opportunities to experience the physical freedom of flight. A notable journey in 1931 from Newark to Washington, DC, marked a significant moment in her aviation experiences.
Helen Keller’s Biggest Adventure: Flying the Plane in 1946.
Delve into Helen Keller’s biggest aviation adventures in 1946. As a representative of the American Foundation for the Overseas Blind, Keller took control of the plane while traversing the Mediterranean with her colleague Polly Thomson.
An Extraordinary Flight: Keller’s Gentle Mastery of the Controls
Experience the flight through Helen Keller’s perspective as she communicated the story to a Scottish reporter using hand signals. Discover how her gentle touch on the controls created a serene and steady flying experience, surprising the flight crew.
Beyond Keller: Defying Skepticism in the Skies
Learn about other deaf-blind individuals, including 15-year-old Katie Inman in 2012, who defied skepticism by piloting an aircraft. Despite challenges, these individuals showcased their abilities in the skies.
Powerful Legacy: Keller’s Impact on Perception
Discover Helen Keller’s lasting impact as a writer, communicator, and activist.Her ventures as a pilot played a crucial role in dispelling social stigmas surrounding blindness, making strides toward a more inclusive society.
Conclusion
In a groundbreaking journey in 1946, Helen Keller, the iconic American writer and activist, soared above limitations, piloting a plane from Rome to Paris. Her aviation odyssey began in 1919 as a passenger during the filming of “Deliverance” and evolved with technological progress. Keller’s pinnacle moment occurred in 1946, steering the aircraft across the Mediterranean, showcasing her gentle mastery of the controls. Beyond her feats, the article highlights others, like Katie Inman in 2012, breaking barriers in the skies. Keller’s legacy as a trailblazer transcends aviation, challenging perceptions and fostering inclusivity in society.
FAQs
Did Helen Keller talk?
Helen Keller really wanted to talk with people like everyone else. So, she learned to speak and gave many speeches about her life. She used the Tadoma method, feeling people’s lips and throat with her fingers to “hear” their speech.
How long did Helen Keller live?
Helen Keller passed away on June 1, 1968, in Easton, Connecticut, at 87 years old. She lived in her home, called Arcan Ridge, which she bought in 1936. It was her permanent home until she died.
Did Helen Keller have kids?
Helen Keller didn’t have kids, and she never got married, even though she was engaged once. She got engaged to her secretary, Peter Fagan, a former journalist, in 1916 when she was 36 years old.
Read Also:
More
A Journey Through Misty Severi’s Remarkable Career

Unveiling Misty Severi’s Role as a Breaking News Reporter
Misty Severi has been making waves as a Breaking News Reporter at the renowned Washington Examiner since August 2021. Her remarkable skills and expertise have positioned her as a standout in journalism. Let’s explore her incredible journey!
Early Life and Education
Born and raised in Southern California, Misty pursued a degree in History and Media, fueled by her unwavering dedication to journalism. Driven by an unwavering determination, she transformed her childhood dream of excelling in journalism into a reality. Graduating with distinction in May 2021, Misty’s academic prowess was evident, laying the foundation for her subsequent success.
Unique Reporting Style and Dedication
Misty possesses a unique knack for sharing information in an engaging and distinctive manner. Her dedication and insightfulness make her a standout reporter, always striving for truthfulness and a global perspective. Her relentless curiosity has fueled her quest to enhance her journalistic knowledge.
Driven by Passion and Determination
Growing up in Southern California, Misty’s passion for journalism manifested early on, even while working in restaurants. Her unwavering determination and dedication to the craft propelled her towards becoming a trailblazer in the industry. Investing extensive hours to refine her skills, Misty emerged as a journalist with a unique and creative storytelling approach.
Misty Severi: Diverse Journalism Coverage and Online Presence
Misty Severi is a versatile journalist with a keen focus on a range of topics, including United States military affairs, European and international politics, and the histories of the U.S. and Europe. Notably, at the Washington Examiner, she spearheads breaking news coverage on pivotal events like the British prime minister elections and the royal family happenings, interviewing significant figures like former Prime Minister Liz Truss. Her writing extends across various subjects such as Social Security updates, political races, legal cases, crime, sports, and celebrity news, showcasing her diverse journalistic expertise.
Besides her impactful reporting, Misty stays pretty active on Twitter as @MistySeveri. You’ll catch her sharing not just her articles but also her thoughts and even some personal updates there. She’s got quite a crowd too, with over 500 followers and more than 2,000 tweets! It’s like a direct line to her audience, sparking conversations and interactions. Oh, and she’s also on Muck Rack, which is like her journalism hangout. It helps her connect with other journalists and possible sources, showing how seriously she takes staying in the loop and connected in the industry.
A Pivotal Moment: Coverage of the BLM Protest
An essential turning point in Misty’s career was her coverage of the BLM protest, earning her accolades, including the esteemed “Student of America” award. Her dedication led her to immerse herself in learning about the nation’s history and diversity to further enrich her journalism.
Accolades and Experience
Misty’s exceptional work as a journalist garnered her prestigious awards, such as the “Best Breaking News Story” from the California College Media Association. Her extensive experience includes contributions to various renowned publications and live reporting during significant events like the 2020 election.
Distinctive Storytelling Style
Misty’s reporting style, known for its uniqueness and appeal, transcends mere event reporting, resonating with audiences worldwide. Her stories cover a wide array of topics, aiming to raise awareness and inspire others.
Conclusion:
Misty Severi’s innovative storytelling approach has made a profound emotional impact on readers, setting her apart in the industry as a successful and bold journalist. Her fearlessness in covering diverse topics speaks volumes about her dedication to journalism.
Misty Severi’s journey embodies resilience, dedication, and an unwavering passion for storytelling. Her commitment to truth and her ability to captivate audiences continue to mark her as a standout figure in the world of journalism.
Read Also:
Business
Beware Of Fake Emails And Fake Apple Pay Images

“Unveiling the Deceptive: Exploring Fake Apple Pay Images. Learn how to distinguish genuine from counterfeit visuals associated with Apple Pay, safeguarding your security and finances from potential scams.”
While using Apple Pay, users can use Apple mobile phones to make contactless payments, eliminating the need to swipe credit cards for payment. The user’s credit card and debit card information is stored in the mobile phone in advance, and the user puts his finger on the fingerprint recognition sensor of the mobile phone and closes the mobile phone to the card reader to complete the payment.
In essence, Apple Pay offers individuals a secure and user-friendly payment method online and at physical stores. This renders it an ideal option for those prioritizing security, convenience, and straightforwardness in their payment experiences.
But many reports about iCloud spam, Apple ID phishing, and fake Apple Pay images have been received in recent weeks. Fraudsters send email messages in the name of Apple, which is how they try to retrieve personal information. They are mainly looking for login or payment details. You can think of the consequences yourself, such as hacking your account or making payments with your credit card.
Is Apple Pay safe?
There is no 100% security in the world. It can only be said that Apple has taken security measures as much as possible for the problems that are coming forth at present.
Firstly, the iPhone does not store credit card information. Instead, the card credentials are replaced with a unique token code. The dynamic security code sent to the bank differs whenever you buy something. The key to all this is the Touch ID fingerprint device on the phone. It’s been proven through several generations of iPhones.
Secondly, Apple also emphasizes user privacy. It does not record any transactions generated through Apple Pay or analyze user purchase behavior. That is why “This is the major distinguishing factor between Apple and its rivals.”
Enabling Fingerprint Recognition and Taking Precautions for Lost Devices
When linking Apple Pay to your credit card, it’s essential to activate fingerprint recognition as an added layer of security. In the unfortunate event that your iPhone or iPad goes missing, the first line of defense is Touch ID. By employing this biometric safeguard, you significantly reduce the risk of unauthorized access to your sensitive information.
Taking Swift Action with Lost Devices
In the event of a lost device, there are proactive measures you can take to protect your data. One option is to utilize the “Lost Mode” feature remotely, accessible through either the “Find My iPhone” app or the iCloud.com web page. By doing so, you not only initiate the search for your device but also automatically deactivate Apple Pay, mitigating the chances of any unauthorized transactions.
Safeguarding Your Apple Watch Payments
When it comes to your Apple Watch, a similar level of diligence is crucial. Before utilizing the Apple Pay functionality on the watch, ensure that you activate the device’s lock password. This acts as a barrier against unauthorized access to your payment methods and financial details.
Managing a Lost Apple Watch
Should your Apple Watch ever go missing, you have options at your disposal. Logging into iCloud allows you to take control, while cancelling the Apple Watch payment authorization through your iPhone offers an extra layer of security. It’s worth noting that even if your Apple Watch is offline, as long as the virtual bank card number is deauthorized, the payment function will remain inactive, safeguarding your finances.
Spotting Fake Apple Pay Images: Tips and Tricks
In today’s digital landscape, scams related to Apple Pay have unfortunately become more prevalent. To avoid falling for these scams, knowing how to recognize fake Apple Pay images is essential.
Here are some practical tips to help you recognize counterfeit images and avoid scams.
Examine the Logo:
Keep a keen eye on the Apple Pay logo featured in the image. Authentic Apple Pay logos maintain a consistent appearance across all images and should never be tampered with. Look for the signature white outline, and ensure that the prominent Apple Pay “P” is centrally positioned within the logo.
Spot the Apple Pay Watermark:
Legitimate Apple Pay images always carry the Apple Pay watermark—a small, white “P” nestled in the lower-left corner of the image. This watermark serves as a reliable marker of authenticity.
Confirm the URL:
Authentic Apple Pay images display the official Apple Pay URL, which is apple.com/applepay. If the URL is missing from the image or differs from the established official URL, exercise caution, as this might indicate a potential fake apple pay image.
Assess the Color Palette:
Genuine Apple Pay images adhere to the recognized color scheme of blue, green, and white, consistent with the official branding. If the image incorporates colors other than these, it’s wise to treat it skeptically.
Look for Clear Text:
Authentic Apple Pay images always include conspicuous text affirming their association with Apple Pay. If an image lacks such explanatory text, it’s advisable to approach it cautiously.
Adhering to these practical guidelines can significantly reduce the risk of falling prey to scams involving fraudulent Apple Pay images. Always maintain a vigilant stance and take the time to verify any suspicious images before clicking on them or divulging any personal information. Safeguarding your online interactions is paramount; these tips can play a pivotal role in ensuring digital security.
FAQs
Does Apple Pay refund money?
Typically, you can initiate returns for items purchased through Apple Pay by presenting the receipt. After the merchant completes the refund, the money will be automatically credited to your payment card.
Does Apple Pay show names?
For security, no personal information is viewable during the payment process of Apple Pay.
Can someone steal Apple Pay details?
Indeed, the potential exists for scams to occur through Apple Pay. If a hacker obtains your personal information, they could breach your account and execute unauthorized transactions.
Related Articles:
-

 Top2 years ago
Top2 years ago2022 US House committee releases Trump’s tax returns, capping a years-long battle
-

 News1 year ago
News1 year agoUSPS EMPLOYEE ASSISTANCE PROGRAM SERVICES AND BENEFITS
-

 Top2 years ago
Top2 years agoInterview With Niantic CEO John Niantsullivan
-
 Top1 year ago
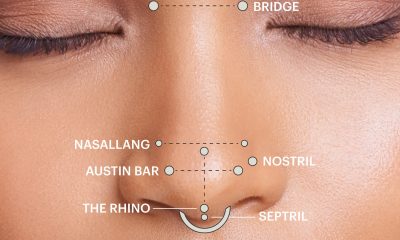
Top1 year agoUnderstanding the Healing Process of Nose Piercings – A Comprehensive Guide
-

 Auto1 year ago
Auto1 year agoTop Porsche Taycan Incentives: Save Big
-

 Business12 months ago
Business12 months agoDoes 7-Eleven Take Apple Pay
-

 Business11 months ago
Business11 months agoBeware Of Fake Emails And Fake Apple Pay Images
-

 Tech1 year ago
Tech1 year agoUSPS LiteBlue ePayroll: A Comprehensive Guide
